How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

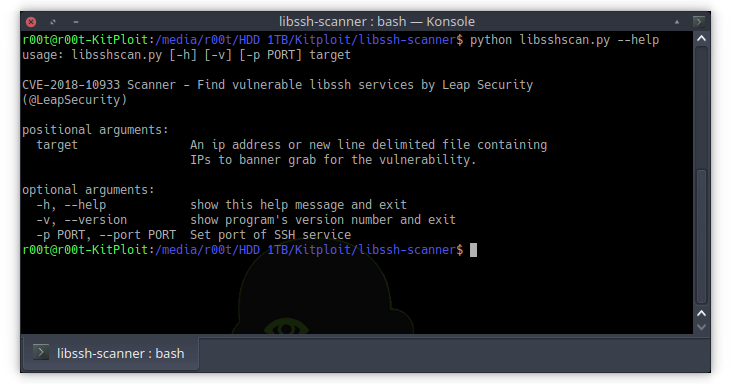
Cisco Talos Intelligence Group - Comprehensive Threat Intelligence: Necro Python bot adds new exploits and Tezos mining to its bag of tricks